instantiator.dev
tech, volunteers, public safety, collective intelligence, articles, tools, code and ideas
- Presence (tool) (in dev)
- ListSky (tool) (in dev)
- The Epistolorean (service)
- Consensus Games (service) (in dev)
- JSON to Smart CSV (tool)
- Escape the Review (profile)
- In this house... (calendar)
- A chat with Lewis (call)
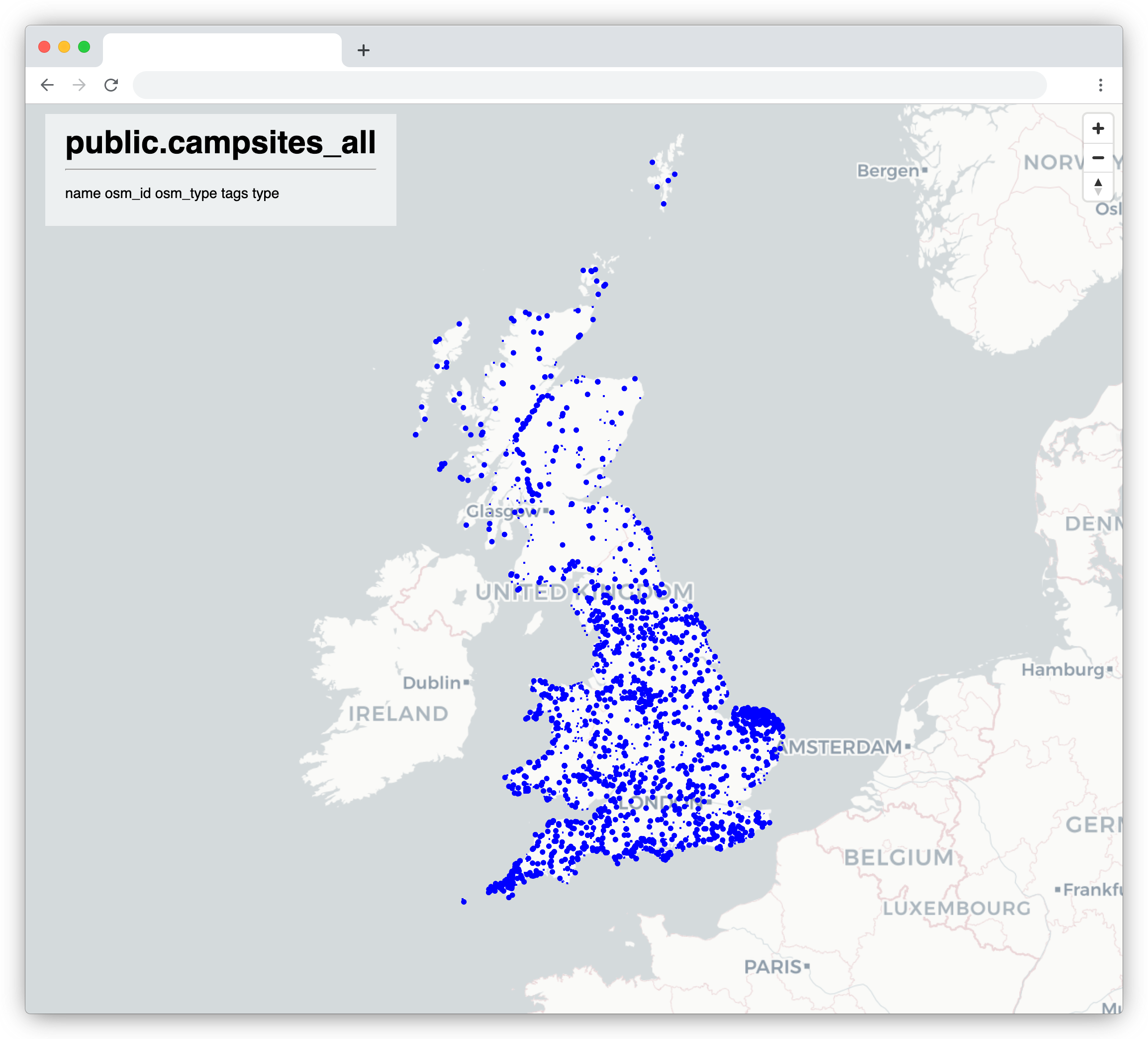
A quick guide to running your own tile server, with a geo database populated from OpenStreetMap data.
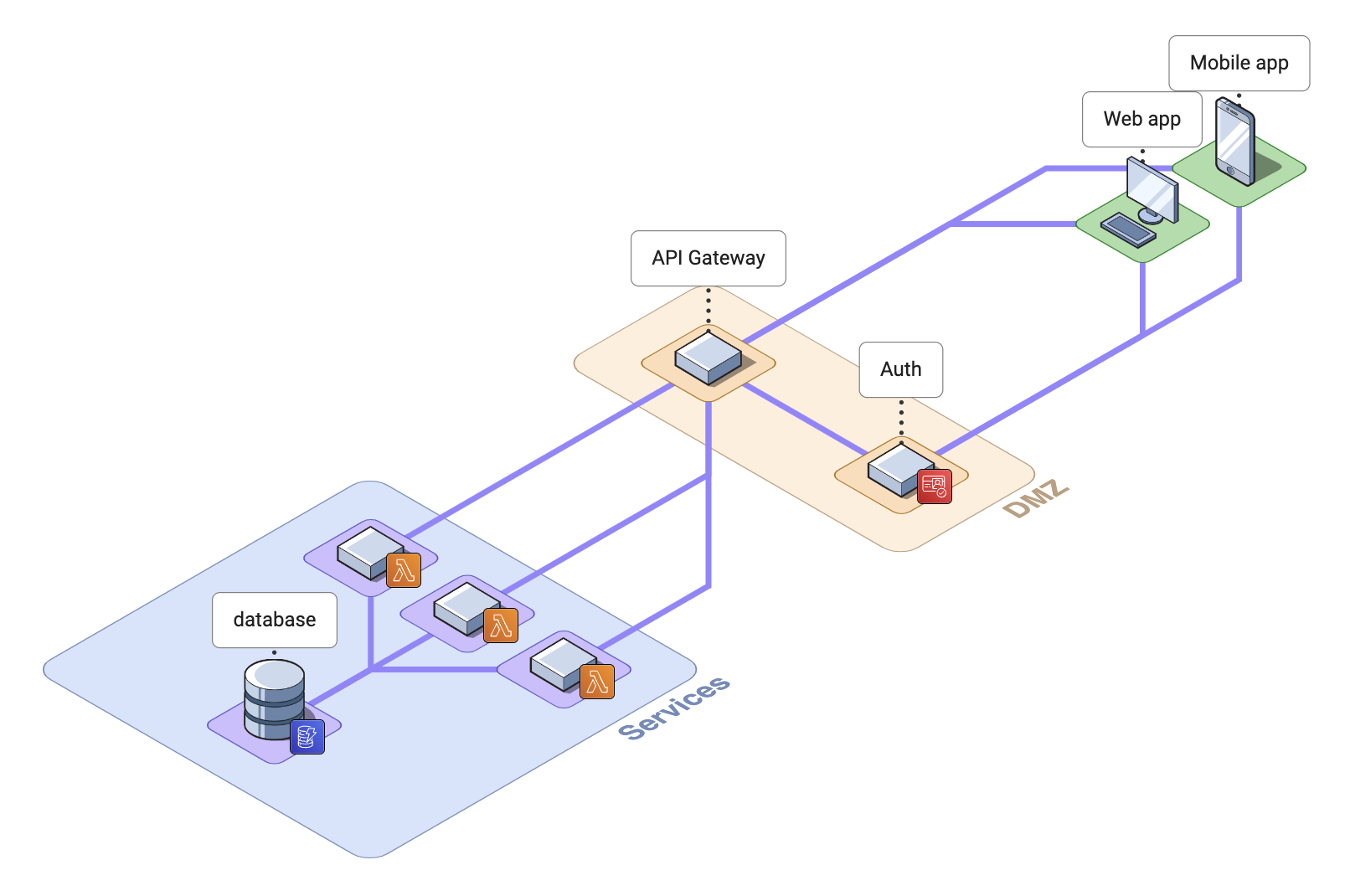
In this part, we’ll build a simple user interface for a Flipper Zero app.
See also:
FlipperZero is a digital signals multi-tool. Here’s a short guide to the basics of building an app for it…
See also:
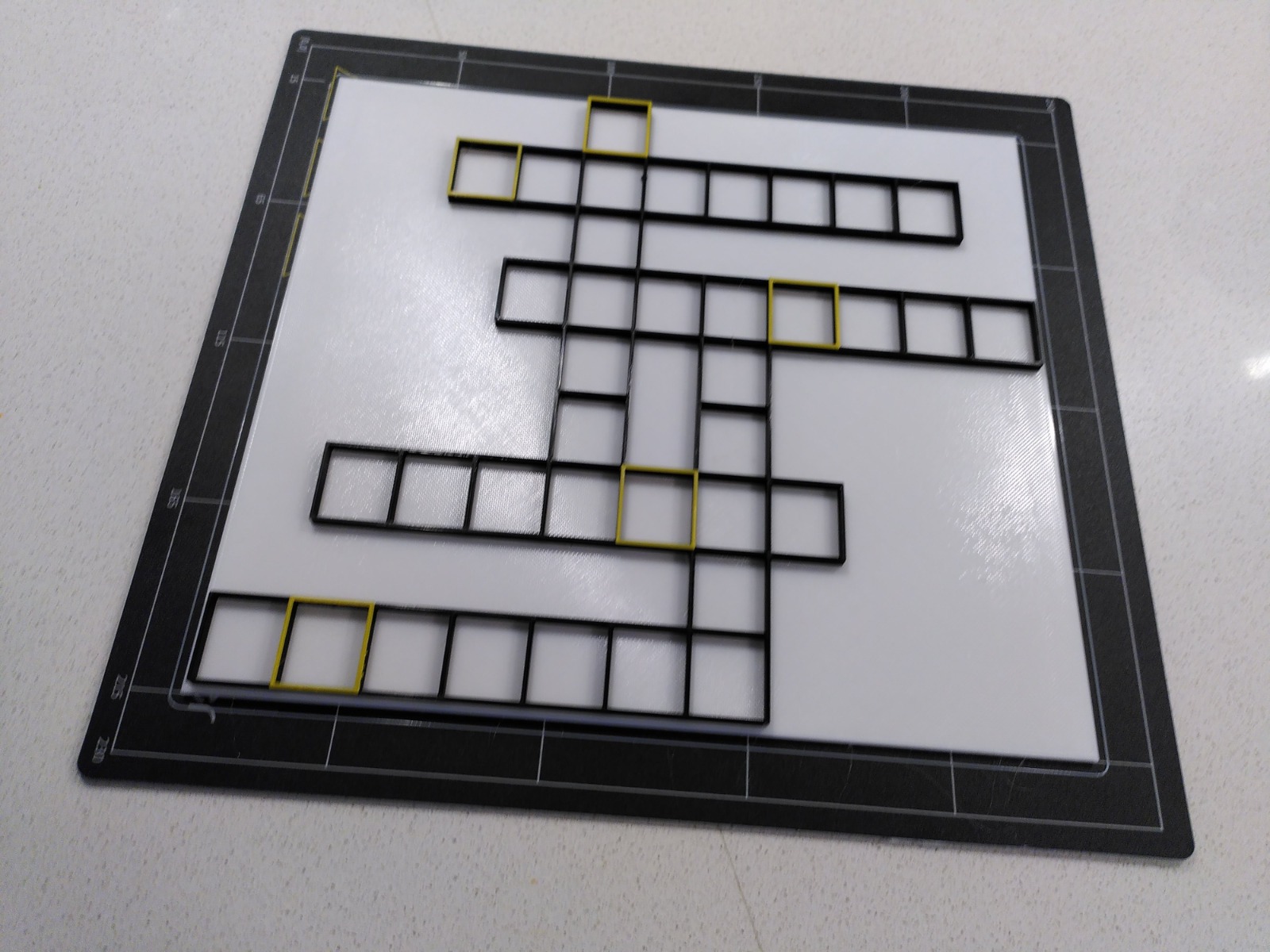
A tool to design 3D printed crossword puzzles.
Generating 3D crossword models
I’ve been working on a tool to generate crossword designs using OpenSCAD. The output is an STL file that you can use with your favourite slicer and send to a 3D printer. It’s open source, and you’re free to plunder it for tips, techniques, or to generate your own…